One of the challenges of iptables, routes, and rules (iprules) is making changes to them permanent. Any changes you make on-the-fly only last until the next system restart. However, there are several ways of making them persist through reboots. Choose one of the methods below to store your changes in user-manageable scripts that are run every time your server is restarted.
Method #1: SystemD Start-up Process
This method presumes you are using a Linux-based operating system utilizing the SystemD system manager and running these updates on a server. The examples and code below were written on Ubuntu 16.04. If you are using a modern Debian distro of Linux, they should work fine. The presence of SystemD is required.
Using this method, you create a hook that calls your script file during the server's startup process. SystemD is required. If you don't know what that is, you should first read this article: What is SystemD?
Prerequisites
You must have prepared scripts available. The examples below presume you have used the same filenames as those in these shell script examples.
If you just rebooted after testing your scripts, make sure you login as root.
sudo -i
Create a .service file. Name it rules.service
nano /etc/systemd/system/rules.service
- Add the following lines. Note the filename matching your first test filename.
[Unit]Description=rules service[Service]ExecStart=/etc/iptables-script.sh[Install]WantedBy=multi-user.target - The script files must be executable. Presuming you did that during your code testing phase, you've already completed this step. If you didn't make them executable earlier, do so now via instructions above under Testing Your Rules.
Setup the service. This will be OK because the scripts flush the caches.
systemctl start rules
You're done! Reboot and confirm your new rules and routes are functioning as expected. If not, review steps above and try again. If they still don't seem to work properly, review Testing Your Rules.
systemctl enable rules
systemctl stop rules
Method #2: Hook into netfilter
If you are using Red Hat or a Debian-based Linux distro, such as Ubuntu 14.04 or later, you may be able to take advantage of a built-in process with hooks connected to netfilter (note: this likely also works on Ubuntu 12.04, but I have not tested it).
This method addresses persistence across reboots of iptables code. Pre-installation of two programs are required: netfilter-persistent and iptables-persistent. netfilter-persistent loads, flushes and saves netfilter rules when the system is booted or halted, while iptables-persistent may be used to load or save iptables changes.
The iptables-persistent program saves the iptables rules currently in memory and sets up a hook in the server's start-up process. When the server is rebooted, the iptables-persistent module is activated, which in turn loads and processes the iptables code in two predefined filenames, if they exist.
netfilter-persistent
netfilter-persistent is a daemon process loaded on system startup. As its name implies, it has hooks into netfilter. It is run during a Linux device's initialization process, after netfilter has loaded. After loading the default iptables rules, and just before exiting, netfilter launches the netfilter-persistent program. In turn, it looks for compatible modules (called "plugins"), and if any are found it loads and executes them. iptables-persistent is one such plugin.
iptables-persistent
iptables-persistent is a modular program launched by netfilter-persistent. Its purpose is to load and save files containing iptables rules.
netfilter-persistent must be installed prior to iptables-persistent
How does it work?
iptables-persistent stores iptables rules in two (2) predefined files, stored in a predetermined location. These files contain instructions for iptables and ip rule. The idea is to save your custom rulesets in these files. One file is dedicated to IPv4 iptables rules, and the other to IPv6 iptables rules.
iptables-persistent file and directory names are hard-coded and cannot be changed
The two filenames and their locations are:
/etc/iptables/rules.v4 for the IPv4 ruleset
/etc/iptables/rules.v6 for the IPv6 ruleset
The iptables-persistent module has two operating modes: automatic and manual.
Automatic Mode
When start-up initialization occurs, its rule files are loaded automatically. These files are not there by default. If the files do not exist, nothing happens. They must be created either manually or via iptables-persistent's Save function, described below.
Manual Mode
It's also possible to manually save an existing rule set in memory to either of the two (2) files and load a rule set from either file into memory. Naturally, these files can be written directly as well. The Save function is a manual process only, and will overwrite existing file contents, but it only writes one file at a time. If you waant to save both, you must choose which file to save, then re-run the program to save the other.
How to Make Use of iptables-persistent
Making use of iptables-persistent is easy.
- Setup your tables, chains, and rules in iptables using standard iptables commands (iptables rules, not routing rules)
- Save your rule set within one of the filenames specified above
- Restart your device, and your ruleset will be loaded automatically when it boots up
Load, Save On Demand
iptables-persistent can also be used to load and save a rule set at any time by invoking the program directly.
If you LOAD a rule set via iptables-persistent, the program will prompt you to choose either the the ipv4 ruleset or the ipv6 ruleset. Your selection will be loaded from the corresponding filename specified above.
If you SAVE a rule set, specify whether you want to save IPv4 or IPv6 rules, and iptables-persistent will save the existing rule set in memory to the corresponding file (IPv4 or IPv6).
iptables-persistent is capable of loading rule sets ONLY from the aforementioned files
"Load" reads the rule set in the indicated filename and loads it into memory for the corresponding iptable (IPv4 or IPv6).
"Save" copies the appropriate current rule set in memory to the corresponding filename (IPv4 or IPv6).
Step-by-Step
Here is an overview of the process, step-by-step:
- Finalize your iptables rules
- Verify netfilter-persistent is installed
- Install and configure iptables-persistent
- Make changes to iptables
- Use a method of saving your iptables configuration
- Reboot
- Verify rule changes are sticky
Installation Walk-thru
Verify netfilter-persistent exists.

When you install iptables-persistent, you will be prompted to establish the initial configuration.
apt install -y iptables-persistentIf you select YES to the first prompt, your existing IPv4 iptables entries will be stored in /etc/iptables/rules.v4

If you select YES to the second prompt, your existing IPv4 ip6tables entries will be stored in /etc/iptables/rules.v6
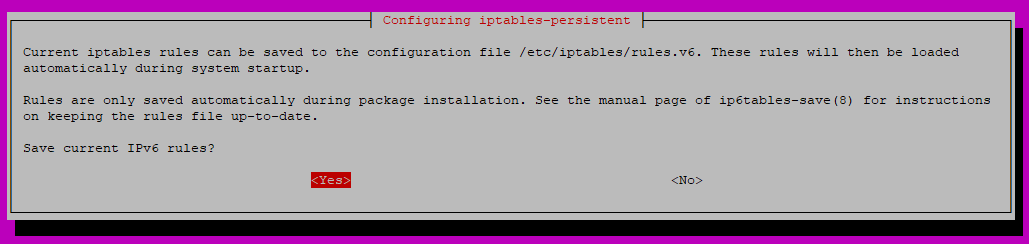
Post-installation screenshot on Ubuntu 16.04:

Verify iptables rules were saved during iptables-persistent configuration at time of installation (screenshot shows ipv4 file contents):

Verify Rules are Sticky
After restarting the device, your rules will be loaded during its startup process from the files noted above. Verify your saved rules are active.
sudo iptables -SRe-launching iptables-persistent Configuration
To re-launch iptables-persistent's configuration utility after it has been installed and run for the first time, you must use dpkg.
sudo dpkg-reconfigure iptables-persistent
